“Hidden” Internet of Things OS proves vulnerable to attack
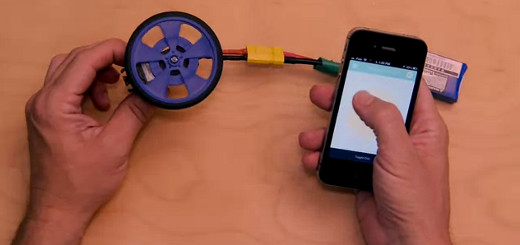
For all the excitement surrounding progress toward networking the everyday machines that make up the “Internet of Things” — tech writers and analysts say the IoT will be a major focus of research and investment this year (as well as a new arena of potential FTC intervention) — there has been comparatively little attention paid to the security risks this increasingly ubiquitous connectivity might entail.
Over the U.S. Thanksgiving holiday, however, the software-security firm Symantec announced the discovery of a worm called Lunix.Darlloz. It is designed to infect Linux for embedded systems, a variant of the open source operating system that often serves as what is sometimes called the “hidden” OS of non-PC “smart” devices – particularly, as the term “hidden” suggests, those designed to conceal software information from users beneath a sheen of consumer-friendly simplicity.
On Symantec’s official blog, Kaoru Hayashi writes that “Symantec has discovered a new Linux worm that appears to be engineered to target the ‘Internet of Things.’ The worm is capable of attacking a range of small, Internet-enabled devices in addition to traditional computers.”
While this worm itself is effectively harmless, and no actual malicious attacks against non-PC devices running embedded Linux have been documented, it does demonstrate the susceptibility of a previously secure and increasingly installed operating system to future attack. This vulnerability is only exacerbated by the fact that, as Hayashi notes, “many users may not realize they are at risk, since they are unaware they own devices that run Linux.”
On one level addressing this problem does appear to be a matter of encouraging consumer awareness, but in truth it’s a more complex issue. Securing these computers against this kind of threat will require changes in design and manufacture as well, as they are generally not intended to accommodate software updates because of the “hidden” nature of the systems as well as simple hardware limitations. This ultimately means that even a user aware of the risk may have no feasible way of taking steps to prevent or repair infection, or even of determining whether a device has been infected in the first place – a concerning prospect in an age when we’re starting to link up everything from our thermostats to our front door locks.
[ Image courtesy of Stuart Miles / FreeDigitalPhotos.net ]